



POTTS is a proof-of-concept implementation of the STARK protocol combined with TRESOR-based Full Disk Encryption. The basic idea behind STARK is that your computer has to prove to you that it is in a certain (non-manipulated) state before you enter your full disk encryption passphrase. The main goal of this method is to render software based Evil Maid Attacks void. Even if the attacker uses tamper and revert attacks.
Every time you boot the system, the computer shows you a secret one-time message (monce) that you have entered before. This message is stored in a way so that the TPM chip of your computer can decrypt the message only if the computer is in the expected state. If and only if the message is the expected one, you then enter the FDE passphrase and a new monce for the next boot. If you follow this scheme strictly, the STARK protocol ensures that an attacker can not create a fake passphrase prompt to trick you into revealing your passphrase and thereby all of your data.
We have prepared a USB drive image that will let you create an encrypted partition and install Arch Linux into it. After the installation the USB drive is used as the boot device.
We use a two-stage boot process. TrustedGRUB is used as boot loader on the USB drive. It measures the Kernel and initrd that will be loaded (stage 1). The initrd contains our UI, authentication is performed in user space. The secret messages are stored on the USB drive as well (decryptable only if the system is in a trusted state). If authentication is successful, the real system (stage 2) is started (via kexec).
The main components of our package are:
To run POTTS you need a computer with a x86_64 CPU and a TPM chip. The system must be able to boot from a MBR style formatted USB drive.
Before you download the full image you should make sure that your system is compatible with TrustedGRUB first.
Download: tgrub-test.img.gz (93 kB)
To install this image onto a USB drive (assuming /dev/sdc):
gzip -d < tgrub-test.img | dd of=/dev/sdc
When you try to boot your target machine with this stick, the screen should look like this:
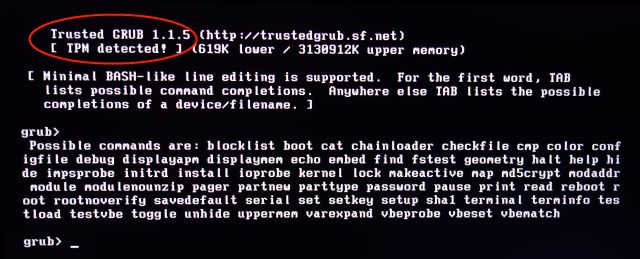
The most important part in this photo is "[ TPM detected! ]". (To reproduce the lower half of this photo, press the Tab key.)
If the machine shows "[ No TPM detected! ]", TPM is either disabled or misconfigured (see the manual for details), or your machine lacks a TPM chip.
If the machine keeps rebooting or has other problems, your machine either lacks a TPM chip or TrustedGRUB is incompatible with your system.
If you are absolutely sure that your system does fulfill the requirements and still have problems, feel free to contact us.
Download: potts-usb.img.gz (344 MB)